When setting up a smart card with Kleopatra you have to import your own public key after deleting the key pair.
In this case it makes no sense to ask for certification of the key.
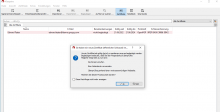
But the "you have imported a new certificate" Window - "Do you want to certify?" pops up anyway.
Can we stop this from happening if a smart card with the corresponding secret key is connected?
Additional difficulty: quite often, Kleopatra recognizes the secret key on the smartcard only after hitting F5.