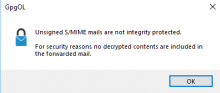
It is possible that an attacker could insert data before and after the plaintext of an unsigned encrypted S/MIME mail. In combination with HTML and Image downloading / active content in HTML an attacker could access the plaintext of a mail.
To mitigate:
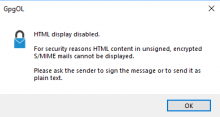
- If an S/MIME Mail is unsigned: Prefer the Text part over the HTML part regardless of the settings if the mail is multipart/alternative.
- If an S/MIME Mail is unsigned and has attachments or is HTML only: Show a big yes/no warning that an attacker might gain the plaintext because the message is unsigned.
The warning should help to educate users that they need to sign and encrypt S/MIME mails and that encrypting is not enough to ensure confidentiality of S/MIME.
To clarify. By unsigned we mean that it does not follow the mime structure:
- Encrypted
- multipart/signed
- content.
- multipart/signed