According to GMT 0003.5-2012, Z hash calculation is added in the SM2 signature algorithm step to solve the problem of mutual signature verification with other libraries such as openssl
Description
Details
- Version
- 1.9.2
Related Objects
- Mentioned Here
- rC6b55246c7708: Add elliptic curve SM2 implementation.
Event Timeline
We need more information on the why and when of this change. We don't want to maintain different versions of the same algorithm. The I-D expired more than 6 years ago and thus it should not be used as a reference.
Some information:
SM2 (GM/T 0003-2012): elliptic curve cryptographic schemes including digital signature scheme, public key.
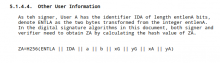
According to the newest original formal standard "GM/T 0003.2 Public key cryptographic algorithm SM2 based on elliptic curves -- Part 2: Digital signature algorithm" by China National cryptography Bureau, it does have a calculate about Z_a.
Z_A=H_256(ENTL_A || ID_A || a || b || x_G || y_G || x_A || y_A)
The standard do not have any update since 2012. So the I-D seems not expired at all.
And I found a blog seems written by the SM2 implementation author of libgcrybt -- Tianjia Zhang. He/She drew a red circle on a standard picture of the Z_A.
Maybe we could contact with him.
rC6b55246c7708: Add elliptic curve SM2 implementation.
@bobwxc wrote:
And I found a blog seems written by the SM2 implementation author of libgcrybt -- Tianjia Zhang. He/She drew a red circle on a standard picture of the Z_A.
Excuse me, where is the link to this blog you mentioned?
https://blog.csdn.net/openanolis/article/details/109745157 (only Chinese)
Author marked as "OpenAnolis" which is a blog of Alibaba Cloud. Zhang also from Ali.
This article mentioned the experience and commit of adding SM2 to libgcrypt and thanks NIIBE Yutaka's help.
Reading through the report, the spec., and current implementation, I concluded that this is not a bug, thus, I'm closing this.
This was basically from confusion, assuming it's not implemented.
In fact, it is implemented. See libgcrypt/tests/basic.c by the function check_pubkey_sign_ecdsa. There are two test cases with sm2 with sm3 hash.